Menopause workers, goodbye to employment if there is no help in the office
ROME – Between insomnia, palpitations and paturnia, working during menopause can be a disabling factor. But –
In Treviso over 300 people attended to discuss sports work. Nepi Molineris: “The world changes, let’s bring sport into the new era”
“Even from meetings like these we must look to the future of a sport that is changing.
On the Iran and Israel issues, the market is like a frog in boiling water – FT Chinese
The recent escalation of tensions between Iran and Israel has left national security experts and financial market
Popular Stories

Skebby’s Messaggioteca service
Skebby, the leading Italian platform in mobile marketing services, has announced the launch of Messaggioteca, a new

Menopause workers, goodbye to employment if there is no help in the office
ROME – Between insomnia, palpitations and paturnia, working during menopause can be a disabling factor. But –

In Treviso over 300 people attended to discuss sports work. Nepi Molineris: “The world changes, let’s bring sport into the new era”
“Even from meetings like these we must look to the future of a sport that is changing.

On the Iran and Israel issues, the market is like a frog in boiling water – FT Chinese
The recent escalation of tensions between Iran and Israel has left national security experts and financial market
Travel & Explore the world

Skebby’s Messaggioteca service
Skebby, the leading Italian platform in mobile marketing services, has announced the launch of Messaggioteca, a new

Menopause workers, goodbye to employment if there is no help in the office
ROME – Between insomnia, palpitations and paturnia, working during menopause can be a disabling factor. But –

In Treviso over 300 people attended to discuss sports work. Nepi Molineris: “The world changes, let’s bring sport into the new era”
“Even from meetings like these we must look to the future of a sport that is changing.

On the Iran and Israel issues, the market is like a frog in boiling water – FT Chinese
The recent escalation of tensions between Iran and Israel has left national security experts and financial market

Xiaohongshu REDlabel Partners with VOGUE for Young Designer Support Program 2024
Xiaohongshu REDlabel Partners with VOGUE China Fashion Fund 2024 to Support Young Designers In an exciting announcement,
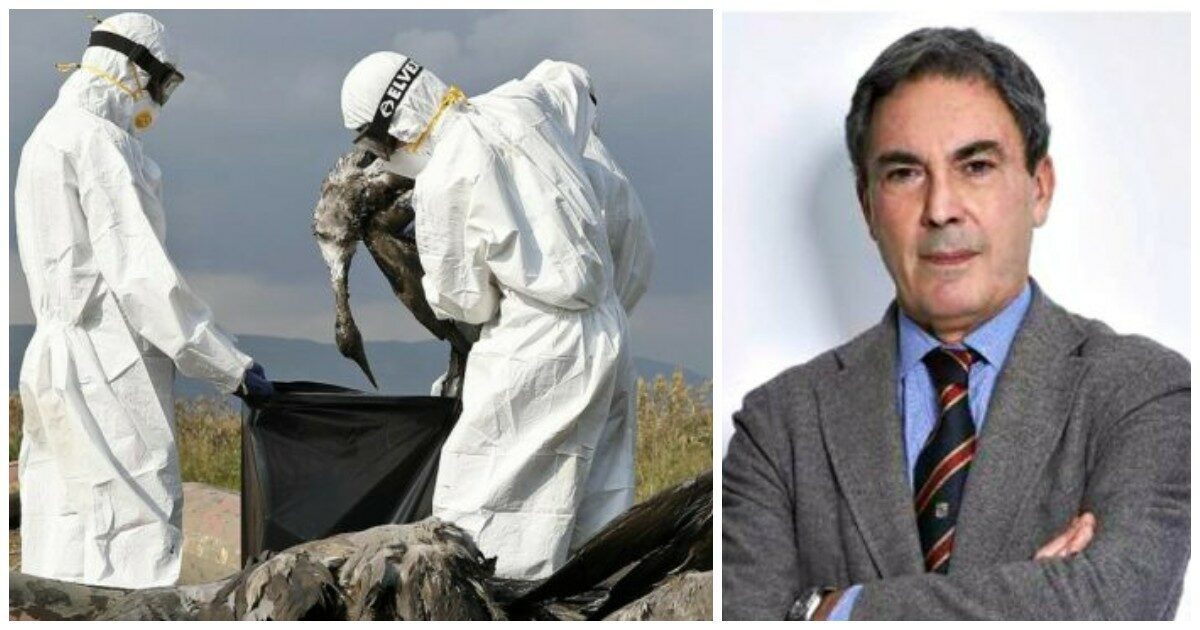
Avian flu, virologist Clementi: “Already a double jump in species. If farm animals are infected with the virus it becomes easier”
The recent emergence of bird flu in the United States and Europe has raised concerns among health

Day of the Saxons: Sebnitz is planning a festival mile to the Czech Republic
The preparations for the Day of the Saxons in Sebnitz are becoming concrete. The festival doesn’t start