In a previous blog post, Atlassian introduced a new service for monitoring stolen credentials (username and password combinations) that have fallen into the hands of malicious actors through data breaches by other providers: the Credential Invalidator. Since then, the manufacturer says it has been able to make over 200,000 such combinations unusable for the hackers.
In recent months, a new trend has emerged in the criminal underground of the Internet: theft of sessions on victims’ devices in order to gain unauthorized access to all kinds of accounts, including Atlassian accounts. These session cookies are then traded and shared in criminal circles.
To mitigate this risk, Atlassian now also monitors stolen session cookies and invalidates them, rendering them useless to the hacker.
What are session cookies?
A “session” is used by a website to track the user as he moves between pages and interacts with the website. When logging in, a session cookie is created on the website server, which is deleted when the user logs out.
Thanks to these session cookies, the website “knows” the user, and the user experience runs much better and with less friction. For example, without such a cookie, users would have to re-authenticate themselves each time they call up a different page.
And since session cookies are used all over the web and stored on users’ end devices for good reasons, they have become the target of malicious actors. Session cookies are created with every login, and hackers try to steal this information from victims’ devices to use on their own devices and access protected data with false identities.
Protection against account takeovers in the Atlassian cloud
Atlassian collects information about stolen sessions and takes action by deleting all sessions of the affected users. As a result, the stolen information is immediately worthless and useless for the hacker. The users, in turn, only have to log in again.
As of January 2023, Atlassian has taken action on over 25,000 session cookies found in third-party data breaches. The process of collecting and handling such information is automated.
What customers can do when managing sessions
Atlassian offers admins various controls to manage sessions. Several new features help fight session cookie theft. Users on the customer side can change their passwords as usual via “Manage Profile”. However, this action now logs the user out of the active session used to change the password. Cloud customers can set a new password in the Security section of account settings configure.
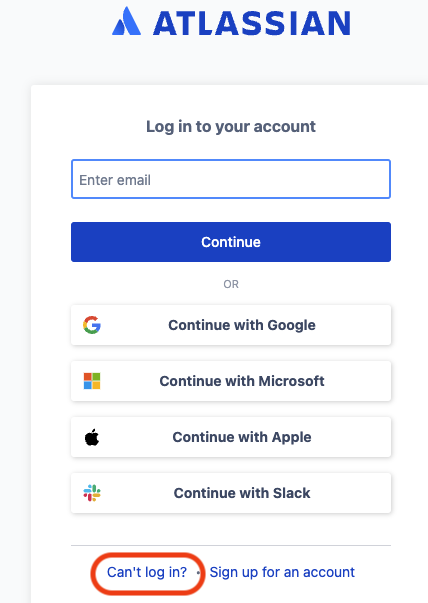
If a customer forgets their password, they can use the “Can’t log in?” link. on the login screen to reset their password. This automatically disables all active sessions.
Customers can view their active sessions across the devices they are using at any time by Click on “Recent Devices” in the Security section of the account settings.
Organization admins have the option to Configure inactivity session timeout in admin settings. From the admin console it is also possible to reset all sessions for the configured authentication policy. This will log out all members of the policy within ten minutes.
Atlassian-ID-Accounts absichern
From a security perspective, it definitely makes sense to enable multi-factor authentication (MFA) for Atlassian cloud users. This is a login process that involves more steps than just entering your password.
For example, users must also enter a code that is generated by a mobile app on the smartphone. The relevant section of the Atlassian documentation explains step by step, How to set up MFA. It definitely offers extra protection.
The ability to manage sessions appropriately and effectively is a useful tool in terms of the organization’s broader security strategies. Atlassian takes security issues very seriously and works hard to keep up with threat developments. By implementing the monitoring of session cookies in the cyber underworld, the manufacturer is taking up another risk trend and ensuring that new threats are minimized as much as possible.
The future for Atlassian customers is in the cloud
Atlassian will end support for its server products in February 2024. So use the remaining time and find out about moving to the cloud. Or even better: just try them out: with ours Cloud Migration Trial you can test Atlassian Cloud yourself and gain initial experience without affecting your existing production system.
Have you made your decision to go to the cloud and want to find out if your business is ready to make the switch? Then we recommend that you read through our short Cloud-Quiz to click: In only eleven questions it turns out whether and how “ready for migration” your organization is! It is also worth finding out more about “data protection in the cloud” before migrating. Together with the data protection expert Thomas Rosin we have some information for you here as well as one practical flight plan compiled with all steps.
Further information
Seven security practices for modern cloud software that are non-negotiable
Atlassian Cloud and identity and access management
Security at scale with Mobile Application Management for Atlassian Cloud
Atlassian Cloud and Securing the Cloud Architecture
